Igay69. Om |work| | No Sign-up |
2. Technical Details • WHOIS: <Registrar>, <Creation Date>, <Privacy‑Protected> • DNS: A = <IP>, NS = <nameservers> • SSL: <Self‑signed / Let’s Encrypt>, TLS version: TLS 1.2 • Hosting: <Provider> (IP belongs to <AS number>, location: <Country>)
1. Summary • Domain: igay69.om • Category: Adult / Potentially Unwanted Content • Observed Risk: High (malvertising, possible drive‑by exploits) igay69. om
Never open the site on a production machine or with privileged accounts. Use a disposable virtual machine with snapshot capability. 7. Mitigation & Defensive Recommendations | Situation | Recommendation | |-----------|----------------| | Personal browsing | Install a reputable ad‑blocker (e.g., uBlock Origin), enable HTTPS‑Only mode, and consider a DNS‑based filter (e.g., Quad9, Cloudflare 1.1.1.3). | | Enterprise network | Block the .om TLD for adult content using a web‑filter (e.g., Cisco Umbrella, Zscaler). Add igay69.om to a blacklist and monitor DNS queries for similar patterns. | | Parental controls | Use DNS‑based familiesafe services (OpenDNS FamilyShield) and enable safe‑search on major search engines. | | Security research | Keep all sandbox images up‑to‑date, and submit any malicious payloads you discover to VirusTotal and relevant malware‑share platforms (e.g., MalwareBazaar). | | Incident response | If a user reports infection after visiting the domain, collect logs (proxy, firewall, DNS), isolate the endpoint, and run a full malware scan with an EDR solution. | 8. Frequently Asked Questions (FAQ) | Q | A | |---|---| | Is igay69.om definitely malicious? | Not definitively—there’s no single “malicious” label, but the content category and typical ad‑network behavior give it a high risk rating. | | Can I safely view the site? | Only inside an isolated sandbox or a VM with no network access to your internal resources. Even then, the site may attempt to download unwanted files. | | What if the site hosts illegal content? | Accessing illegal material is a criminal offense in many jurisdictions. If you suspect illegal content, report it to local law enforcement or to the hosting provider. | | How do I report the domain? | Most major security vendors accept abuse reports (e.g., Google Safe Browsing, PhishTank, Spamhaus). You can also file a complaint with the .om registry (Telecommunications Regulatory Authority – Oman). | | Will blocking the domain affect legitimate users? | Only if they intentionally need adult content for research or medical reasons. In most corporate or public environments, blocking is advisable. | 9. Sample “Threat‑Intel” Report Template (For Your Own Use) Below is a concise template you can copy‑paste into a document or ticketing system: Use a disposable virtual machine with snapshot capability
Title: Threat Intel – igay69.om (Adult‑Content Site) | | Enterprise network | Block the
| Step | Action | Tools / Tips | |------|--------|--------------| | | Resolve the domain, record the IP, note any CNAME chains. | dig , nslookup , whois , dnsviz | | 2. Reputation Check | Query multiple threat‑intel feeds. | VirusTotal (URL & IP), AbuseIPDB, URLhaus, Spamhaus DBL, Cisco Talos, Hybrid Analysis | | 3. Sandbox Fetch | Retrieve the page in a detached, virtual environment (no network bridge to your main workstation). | Cuckoo Sandbox, REMnux, Any.run, FireEye Threat Analyst | | 4. Static Analysis | Download the HTML source, examine scripts, iframes, and external resources. Look for obfuscated JavaScript, base64 strings, or known malicious payload signatures. | wget --no-robots -O page.html , js-beautify , grep for suspicious patterns | | 5. Network Capture | While loading the page in the sandbox, capture all HTTP/HTTPS traffic. Identify any redirects to known malware domains, suspicious download URLs, or data exfiltration. | Wireshark, tcpdump , mitmproxy (with proper certificates) | | 6. Dynamic Behavior | Observe if the site triggers pop‑ups, downloads, or attempts to execute files. | Sandbox UI logs, process monitor (procmon), Sysmon events | | 7. Threat Intel Enrichment | Correlate observed IPs/URLs with open‑source intel platforms. | MISP, OTX, Passive DNS, Shodan/ZoomEye | | 8. Documentation | Record all findings (screenshots, logs, hash values) in a structured report. | Markdown/HTML report, CVE‑style layout, MITRE ATT&CK mapping if relevant |
3. Reputation Checks • VirusTotal: <URL score>, <IP score> • AbuseIPDB: Score











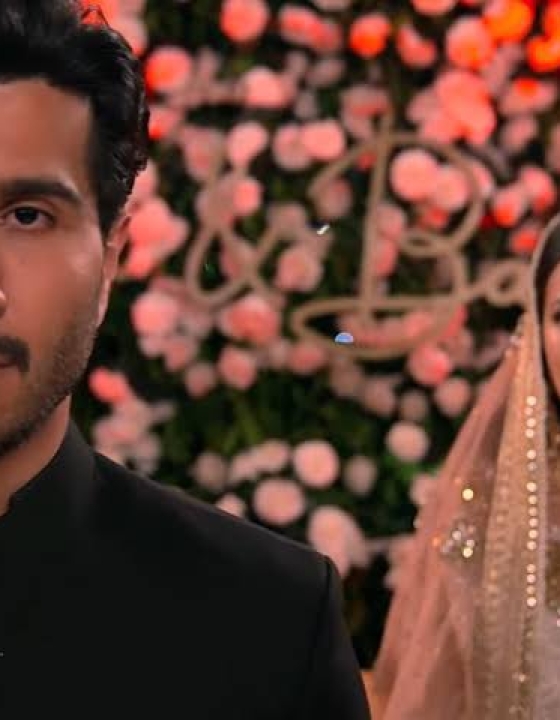



Rita
September 16, 2023This is the second Pakistani serial I have seen. I was so hooked to watching it. Love the characters of Murtasim, handsome man with the eyes that does the talking. Meerab as a stubborn and spoiled brat who fell in love with the guy who adores her and so patient with her because of her contract. Never forced her to do anything and never asserted his rights as a husband. Waiting for her to fall in love . I hated Haya from the start to the end. Beautiful serial. I’m going to watch more of the Murtasim series now.